The HTTPS protocol is a standard security technology used to establish an encrypted link between a web server and a web client. HTTPS facilitates secure network communication by identifying and authenticating the server as well as ensuring the privacy and integrity of all transmitted data. Since HTTPS prevents eavesdropping on or tampering with information sent over the network, it should be used with any login or authentication mechanism and on any network where communication contains confidential or proprietary information.
To encrypt communication between the ArcGIS Web Adaptor and Portal for ArcGIS, the use of HTTPS on port 443 is required. No other port can be used. The use of HTTPS ensures that names, passwords, and other sensitive information cannot be deciphered as they are sent between ArcGIS Web Adaptor and the portal. When you use HTTPS, you connect to your web pages and resources using the HTTPS protocol instead of HTTP.
You need to obtain a server certificate and bind it to the website that hosts ArcGIS Web Adaptor. Each web server has its own procedure for loading a certificate and binding it to a website.
Ensure also that your web server is set to ignore client certificates in order to correctly access secure services over HTTPS.
Create a server certificate
To be able to create an HTTPS connection between ArcGIS Web Adaptor and your portal, the web server requires a server certificate. A certificate is a digital file that contains information about the identity of the web server. It also contains the encryption technique to use when establishing a secure channel between the web server and the portal. A certificate must be created by the owner of the website and digitally signed. There are three types of certificates—CA-signed, domain, and self-signed—which are explained below.
CA-signed certificates
Certificate authority (CA) signed certificates should be used for production systems, particularly if your deployment of Portal for ArcGIS is going to be accessed from users outside your organization. For example, if your portal is not behind your firewall and accessible over the Internet, using a CA-signed certificate assures clients from outside your organization that the identity of the website has been verified.
In addition to being signed by the owner of the website, a certificate may be signed by an independent CA. A CA is usually a trusted third party that can attest to the authenticity of a website. If a website is trustworthy, the CA adds its own digital signature to that website's self-signed certificate. This assures web clients that the website's identity has been verified.
When using a certificate issued by a well-known CA, secure communication between the server and the web client occurs automatically with no special action required by the user. There is no unexpected behavior or warning message displayed in the web browser, since the website has been verified by the CA.
Domain certificates
If your portal is located behind your firewall and using a CA-signed certificate is not possible, using a domain certificate is an acceptable solution. A domain certificate is an internal certificate signed by your organization's certificate authority. Using a domain certificate helps you reduce the cost of issuing certificates and eases certificate deployment, since certificates can be generated quickly within your organization for trusted internal use.
Users within your domain will not experience any of the unexpected behavior or warning messages normally associated with a self-signed certificate, since the website has been verified by the domain certificate. However, domain certificates are not validated by an external CA, which means users visiting your site from outside your domain will not be able verify that your certificate really represents the party it claims to represent. External users will see browser warnings about the site being untrusted which may lead them to think they are actually communicating with a malicious party and be turned away from your site.
Create a domain certificate in IIS
In IIS Manager, do the following to create a domain certificate:
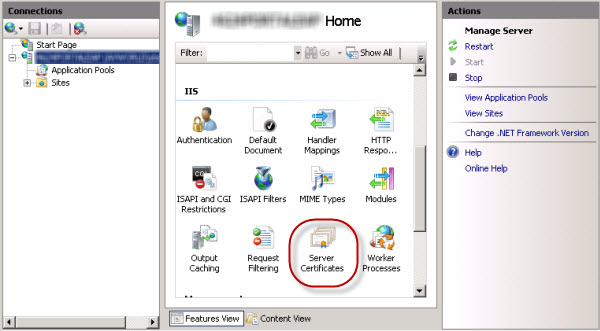
- In the Connections pane, select your server in the tree view and double-click Server Certificates.
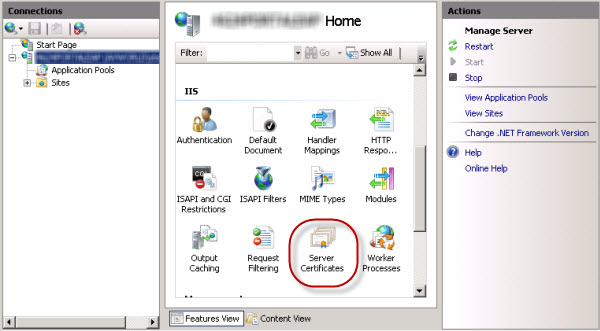
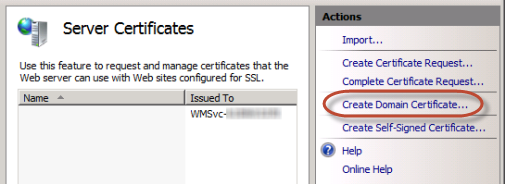
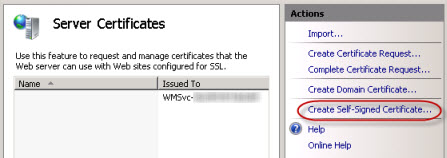
- In the Actions pane, click Create Domain Certificate.
- In the Distinguished Name Properties dialog box, enter the required information for the certificate:
- For the Common name, you must enter the fully qualified domain name of the machine, for example, portal.domain.com.
- For the other properties, enter the information specific for your organization and location.
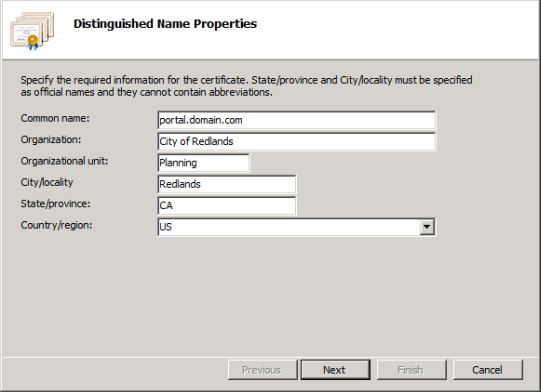
- Click Next.
- In the Online Certification Authority dialog box, click Select and choose the certification authority within your domain that will sign the certificate. If this option is unavailable, enter your domain certification authority in the Specify Online Certification Authority field, for example, City Of Redlands Enterprise Root\REDCASRV.empty.local. If you need help with this step, consult your system administrator.
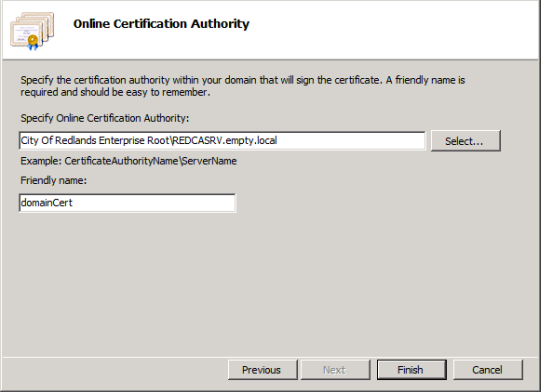
- Enter a user-friendly name for the domain certificate and click Finish.
The final step is for you to bind the domain certificate to HTTPS port 443. See Binding the certificate to the website below for instructions.
Self-signed certificates
Creating a self-signed certificate should not be considered a valid option for a production environment as it will lead to unexpected results and a poor experience for all users of the portal.
A certificate signed only by the owner of the website is called a self-signed certificate. Self-signed certificates are commonly used on websites that are only available to users on the organization's internal (LAN) network. If you communicate with a website outside your own network that uses a self-signed certificate, you have no way to verify that the site issuing the certificate really represents the party it claims to represent. You could actually be communicating with a malicious party, putting your information at risk.
When you first set up the portal, you might use a self-signed certificate to do some initial testing to help you quickly verify that your configuration was successful. However, if you use a self-signed certificate, beware that you will experience the following when testing:
- Web browser and ArcGIS Desktop warnings about the site being untrusted. When a web browser encounters a self-signed certificate, it will typically display a warning and ask you to confirm that you want to proceed to the site. Many browsers display warning icons or a red color in the address bar as long as you are using the self-signed certificate. You should expect to see these type of warnings if you configure your portal with a self-signed certificate.
- Inability to open a federated service in the portal map viewer, add a secured service item to the portal, log in to ArcGIS Server Manager on a federated server, and connect to the portal from Esri Maps for Office.
- Unexpected behavior when printing hosted services and accessing the portal from client applications.
- Inability to sign in to the portal from Esri Maps for Office unless the self-signed certificate is installed into the Trusted Root Certification Authorities certificate store on the machine running Esri Maps for Office.
Uwaga:
The above list of issues you will experience when using a self-signed certificate is not exhaustive. It is recommended that you use a domain certificate or CA-signed certificate to fully test and deploy your portal.
Create a self-signed certificate in IIS
In IIS Manager, do the following to create a self-signed certificate:
- In the Connections pane, select your server in the tree view and double-click Server Certificates.
- In the Actions pane, click Create Self-Signed Certificate.
- Enter a user-friendly name for the new certificate and click OK.
The final step is for you to bind the self-signed certificate to HTTPS port 443. See Binding the certificate to the website below for instructions.
Bind the certificate to the website
Once you've created a certificate, you'll need to bind it to the website hosting ArcGIS Web Adaptor. Binding refers to the process of configuring the certificate to use port 443 on the website. The instructions for binding a certificate with the website vary depending on the platform and version of your web server. For instructions, consult your system administrator or your web server's documentation. For example, the steps for binding a certificate in IIS are below.
Bind a certificate to port 443 in IIS
In IIS Manager, do the following to bind a certificate to HTTPS port 443:
- Select your site in the tree view and in the Actions pane, click Bindings.
- If port 443 is not available in the Bindings list, click Add. From the Type drop-down list, select https. Leave the port at 443.
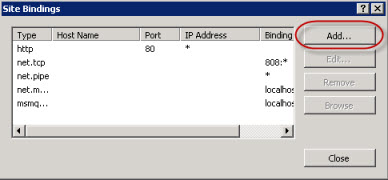
- If port 443 is listed, select the port from the list and click Edit.
- If port 443 is not available in the Bindings list, click Add. From the Type drop-down list, select https. Leave the port at 443.
- From the certificate drop-down list, select your certificate name and click OK.

Test your site
After binding the certificate to the website, you can configure your Web Adaptor for use with the portal. You will need to access the ArcGIS Web Adaptor configuration page using an HTTPS URL such as https://webadaptorhost.domain.com/webadaptorname/webadaptor.
After you've configured your Web Adaptor, you should test that HTTPS is working properly by making an HTTPS request to the portal website, for example, https://webadaptorhost.domain.com/webadaptorname/home. If you are testing with a self-signed certificate, dismiss the browser warnings about untrusted connections. This usually involves adding an exception to your browser so that it will allow you to communicate with the site that is using a self-signed certificate.
To learn more about using SSL in your portal deployment, see Security best practices.