You can configure NetIQ Access Manager 3.2 and later versions as your identity provider for enterprise logins in Portal for ArcGIS. The configuration process involves two main steps: registering your enterprise identity provider with Portal for ArcGIS and registering Portal for ArcGIS with the enterprise identity provider.
Optionally, you can provide metadata to the portal about the enterprise groups in your identity store. This allows you to create groups in the portal that leverage the existing enterprise groups in your identity store. When members log in to the portal, access to content, items, and data are controlled by the membership rules defined in the enterprise group. If you do not provide the necessary enterprise group metadata, you'll still be able to create groups. However, membership rules will be controlled by Portal for ArcGIS, not the identity store.
Required information
Portal for ArcGIS requires certain attribute information to be received from the identity provider when a user logs in using enterprise logins. NameID is a mandatory attribute that must be sent by your identity provider in the SAML response to make the federation with Portal for ArcGIS work. When a user from the IDP logs in, a new user with the user name NameID will be created by Portal for ArcGIS in its user store. The allowed characters for the value sent by the NameID attribute are alphanumeric, _ (underscore), . (dot), and @ (at sign). Any other characters will be escaped to contain underscores in the user name created by Portal for ArcGIS.
Portal for ArcGIS supports flow-in of the givenName and the email address attributes of the enterprise login from the enterprise identity provider. When a user signs in using an enterprise login, and if Portal for ArcGIS receives attributes with the names givenname and email or mail (in any case), Portal for ArcGIS populates the full name and the email address of the user account with the values received from the identity provider. It's recommended that you pass in the email address from the enterprise identity provider so the user can receive notifications.
Register NetIQ Access Manager as the enterprise identity provider with Portal for ArcGIS
- Sign in to the portal website as an Administrator of your organization and click My Organization > Edit Settings > Security.
- Within the Enterprise Logins section, click the Set Identity Provider button and enter your organization's name in the window that opens (for example, City of Redlands). When users access the portal website, this text displays as part of the SAML sign in option (for example, Using your City of Redlands account).
- Choose if your users will be able to join the organization Automatically or After you add the accounts to the portal. Selecting the first option enables users to sign in to the organization with their enterprise login without any intervention from an administrator. Their account is registered with the organization automatically the first time they sign in. The second option requires the administrator to register the necessary accounts with the organization using a command line utility or sample Python script. Once the accounts have been registered, users will be able to sign in to the organization.
Tip:
It's recommended that you designate at least one enterprise account as an administrator of your portal and demote or delete the initial administrator account. It is also recommended you disable the Create an account button and sign-up page (signup.html) in the portal website so people cannot create their own accounts. For full instructions, see Configuring a SAML-compliant identity provider with your portal.
- Configure the advanced settings as applicable:
- Encrypt Assertion—Select this option if NetIQ Access Manager will be configured to encrypt SAML assertion responses.
- Enable Signed Request—Select this option to have Portal for ArcGIS sign the SAML authentication request sent to NetIQ Access Manager.
- Logout URL—Update this value if you have configured NetIQ Access Manager to use a custom log out URL.
- Entity ID—Update this value to use a new entity ID to uniquely identify your portal to NetIQ Access Manager.
The Encrypt Assertion and Enable Signed Request settings use the certificate samlcert in the portal keystore. To use a new certificate, delete the samlcert certificate, create a new certificate with the same alias (samlcert) following the steps in Import a certificate into the portal, and restart the portal.
- Provide metadata information for the identity provider using one of the three options below:
- URL—Choose this option if the URL of NetIQ Access Manager federation metadata is accessible by Portal for ArcGIS. The URL is usually http(s)://<host>:<port>/nidp/saml2/metadata on the machine where NetIQ Access Manager is running.
Note:
If your enterprise identity provider includes a self-signed certificate, you may encounter an error when attempting to specify the HTTPS URL of the metadata. This error occurs because Portal for ArcGIS cannot verify the identity provider's self-signed certificate. Alternatively, use HTTP in the URL, one of the other options below, or configure your identity provider with a trusted certificate.
- File—If the URL is not accessible by Portal for ArcGIS, save the metadata obtained from the URL above as an XML file and upload the file.
- Parameters—Choose this option if the URL or file is not accessible. Enter the values manually and supply the requested parameters: login URL and certificate. Contact your NetIQ Access Manager administrator to obtain these.
- URL—Choose this option if the URL of NetIQ Access Manager federation metadata is accessible by Portal for ArcGIS. The URL is usually http(s)://<host>:<port>/nidp/saml2/metadata on the machine where NetIQ Access Manager is running.
- Optionally provide metadata to the portal about the
enterprise groups in the identity store:
- Sign in to the ArcGIS Portal Directory as an Administrator of your organization. The URL is in the format https://webadaptor.domain.com/arcgis/portaladmin.
- Click Security > Config > Update Identity Store.
- Place the group configuration JSON in the Group store configuration (in JSON format) text box.
Copy the following text, and alter it to contain the information specific to your site:
{ "type": "LDAP", "properties": { "userPassword": "secret", "isPasswordEncrypted": "false", "user": "uid=admin\,ou=system", "ldapURLForUsers": "ldap://bar2:10389/ou=users\,ou=ags\,dc=example\,dc=com", "ldapURLForRoles": "ldap://bar2:10389/dc=example,dc=com", "usernameAttribute": "cn", "caseSensitive": "false", "userSearchAttribute": "cn", "memberAttributeInRoles": "member", "rolenameAttribute":"cn" } }In most cases, you'll only need to alter values for the user, userPassword, ldapURLForUsers, and ldapURLForUsers parameters. The URL to your LDAP will need to be provided by your LDAP administrator. The account you use for the user parameter needs permissions to look up the names of groups in your organization. Although you type the password in clear text, it will be encrypted when stored in the portal's configuration directory or viewed.
If your LDAP is configured to be case insensitive, set the caseSensitive parameter to "false".
- When you finish entering the JSON for the user store configuration, click Update Configuration to save your changes and restart the portal.
Register Portal for ArcGIS as the trusted service provider with NetIQ Access Manager
- Configure an attribute set.
Follow the steps below to create a new attribute set so the attributes can be sent to Portal for ArcGIS as part of the SAML assertion after authenticating the user. If you have an existing attribute set already configured in your NetIQ Access Manager, you can use that set as well.
- Sign in to NetIQ Access Manager administration console. This is usually available at http(s)://<host>:<port>/nps.
- Browse to your identity server in the NetIQ admin console and click the Shared Settings tab. Under Attribute Sets, you should see any attribute sets you've already created. Click New and create a new attribute set. Enter Portal under Set Name and click Next.
- Define the attribute mappings and add them to the attribute set you created in the previous step.
Portal for ArcGIS supports flow-in of the givenName and the email address attributes of the enterprise login from the enterprise identity provider. When a user signs in using an enterprise login and if Portal for ArcGIS receives attributes with the names givenname and email or mail (in any case), Portal for ArcGIS populates the full name and the email address of the user account with the values received from the identity provider.
It is recommended that you pass in the email address from the enterprise identity provider to Portal for ArcGIS. This helps if the user later becomes an administrator. Having an email address in the account entitles the user to receive notifications regarding any administrative activity and send invitations to other users to join the organization.
Click the New link and add any new attribute mappings. The screen captures below show adding attribute mapping for givenName, email address, and uid. You can choose any attributes from your authentication source instead of these examples.
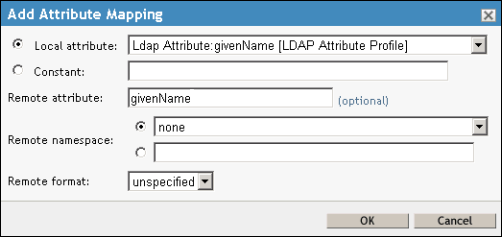
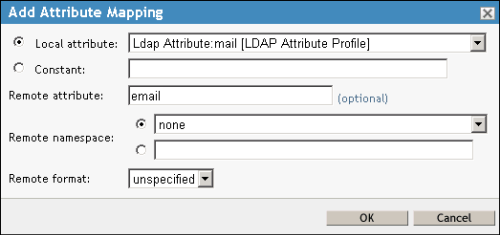
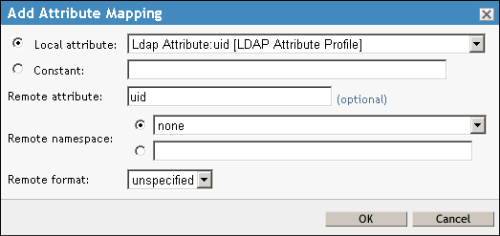
Click Finish within the Create Attribute Set wizard. This creates a new attribute set named Portal.
- Follow the steps below to add Portal for ArcGIS as a trusted provider with NetIQ Access Manager.
- Sign in to the NetIQ admin console, choose your identity sever, and click the Edit link.
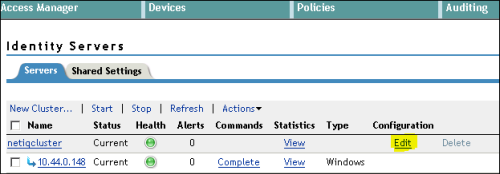
The General tab opens.
- Click the SAML 2.0 tab and click New > Service Provider.
The Service Provider window is where you add Portal for ArcGIS as a trusted service provider with NetIQ Access Manager.
- In the Create Trusted Service Provider wizard, click Metadata Text as the Source and paste the metadata of your Portal for ArcGIS organization within the Text box.
Get the metadata of your Portal for ArcGIS organization by logging in to your organization as an administrator, clicking the Edit Settings button, the Security tab, and the Get Service Provider button. Save the metadata as an XML file.
Click Next and Finish to finish adding the trusted service provider.
- Sign in to the NetIQ admin console, choose your identity sever, and click the Edit link.
- Follow the steps below to configure Portal for ArcGIS and NetIQ Access Manager federation properties.
- In the SAML 2.0 tab, click the service provider link under Service Providers. The Configuration tab opens. Click the Metadata tab and verify that the metadata for your Portal for ArcGIS organization is correct.
- Click the Configuration tab to go back to the Trust section of the configuration. Select the option Encrypt assertions if you chose the advanced setting Encrypt Assertion when registering NetIQ Access Manager as the enterprise identity provider with Portal for ArcGIS.
- Click the Attributes tab.
In this step, you add the attribute mapping from the set you created in step 2.1 so NetIQ Access Manager can send the attributes to Portal for ArcGIS in the SAML assertion.
Select the attribute set you defined in step 2.1 above. After you select your attribute set, the attributes you defined in the set appear in the Available box. Move your givenName and email attributes to the Send with authentication box.
- Click the Authentication Response tab under the Configuration tab of the service provider and set up the authentication response.
Click Post from the Binding drop-down menu.
In the Name Identifier column, check the box next to Unspecified.
In the Default column, select the radio button next to Unspecified.
In the Value column, choose Ldap Attribute uid.
Note:
You can configure any other unique attribute in the attribute set from your authentication source to be sent as NameID. The value of this parameter will be used as the user name in the organization.
Click Apply.
- Under Configuration, click the Options tab and choose your user authentication contract, for example, Name/Password - Form and click Apply.
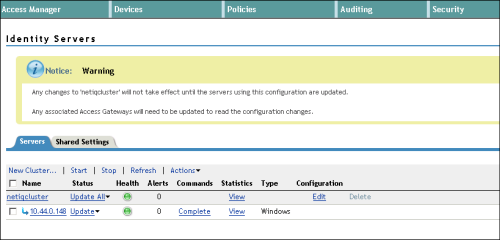
- Restart NetIQ Access Manager by browsing to your identity server and clicking the Update All link.