What does a firewall do?
Every computer has thousands of ports through which other computers can send information. A firewall is a security mechanism that limits the number of ports on your machine through which other computers can communicate. When you use a firewall to restrict communication to a small number of ports, you can closely monitor those ports to prevent an attack. Also, you can configure the firewall to restrict communication to a port known only to you.
Firewalls can be implemented through hardware, software, or a combination of both. Firewalls work best in detecting attacks, such as worms and some Trojan horses, that could enter or leave your system through an open port. They do not protect you from viruses attached to emails or from threats inside your network. Therefore, although firewalls are important, they should not be the only component of your overall security strategy. Antivirus software and solid authentication and authorization techniques are examples of other security strategies that should be deployed in conjunction with firewalls.
Protecting ArcGIS Server with firewalls
There are several appropriate strategies you can take to protect your ArcGIS Server site with firewalls. The following strategies use firewalls to separate your internal network (in which security is regulated) from the external network (in which security cannot be guaranteed).
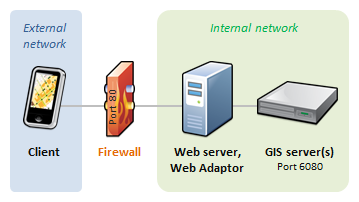
Single firewall
The simpler and less secure of the two options uses a single firewall to restrict traffic to your web server. Usually, only port 80 is left open. Your web server, ArcGIS Web Adaptor, the GIS server, and your data all reside behind the firewall in the secure internal network.
Multiple firewalls with reverse proxy and ArcGIS Web Adaptor in a perimeter network
A more secure, but also more complex, approach is to configure the web server and ArcGIS Web Adaptor within a perimeter network (also known as a demilitarized zone [DMZ] or screened subnet). In this scenario, ArcGIS Web Adaptor receives incoming requests through port 80. It then sends the request through another firewall to the GIS server, using port 6080. ArcGIS Web Adaptor causes the machine to act as a reverse proxy.
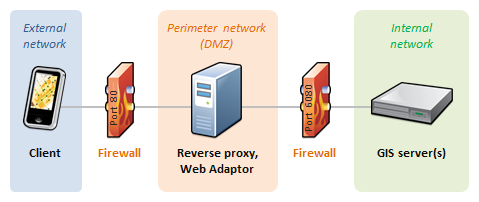
Here's a closer look at each component in this scenario:
- A perimeter network consists of machines that Internet users can access through a firewall but are not part of your secure internal network. The perimeter network isolates the internal network from direct Internet client access.
- The ArcGIS Web Adaptor in the perimeter network receives Internet requests through a common port, such as port 80. A firewall prevents access through any other ports. Then ArcGIS Web Adaptor sends the request to the secure internal network through another firewall using the ArcGIS Server port 6080.
- The GIS server and data server (if there is one) reside in the secure internal network. A request entering the secure network must come from ArcGIS Web Adaptor and pass through a firewall. A response leaving the secure network returns to the client the same way it arrived. First, the response passes back through the firewall to ArcGIS Web Adaptor. Then ArcGIS Web Adaptor sends it through another firewall to the client.
If a machine in the perimeter network somehow becomes compromised, the second firewall reduces the chance that the affected machine can harm machines in your internal network.
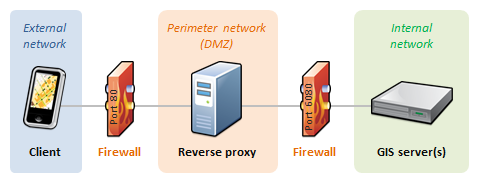
Integrating an existing reverse proxy
If your organization already uses a reverse proxy, you can configure it to route requests to ArcGIS Server on your secure internal network. The most basic option is to connect directly to the GIS server through port 6080 without installing ArcGIS Web Adaptor.
If you want the port between the reverse proxy and your secure internal network to remain unknown, you can install ArcGIS Web Adaptor on another web server within your secure internal network. This ArcGIS Web Adaptor can be configured to accept traffic through a port of your choice.
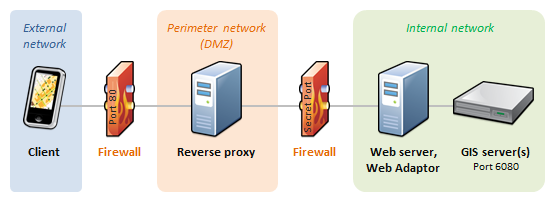
To learn more about how to integrate ArcGIS Server with your reverse proxy server, see Using a reverse proxy server with ArcGIS Server.
Firewalls between GIS server machines
It's typically not necessary to place firewalls between your GIS server machines. However, if you do have firewalls between the machines, you should open the ports listed in Ports used by ArcGIS Server.